What is Trusted Platform Module?
 Trusted Platform Module (TPM) chips are used in all types of computers from personal laptops, to business computers, to industrial panel PCs, to medical computers. TPM secures your data with a secure algorithm integrated into your computer hardware. It provides a higher level of security than software alone and protects your data from hackers, malware and thieves. This is especially important for industrial computers, which can store massive amounts of data about your business, and medical computers, which can store sensitive patient data. TPM is widely accepted as the most secure method of protecting information stored on a computer. This blog provides an overview of TPM and how it is used in industrial and medical computers.
Trusted Platform Module (TPM) chips are used in all types of computers from personal laptops, to business computers, to industrial panel PCs, to medical computers. TPM secures your data with a secure algorithm integrated into your computer hardware. It provides a higher level of security than software alone and protects your data from hackers, malware and thieves. This is especially important for industrial computers, which can store massive amounts of data about your business, and medical computers, which can store sensitive patient data. TPM is widely accepted as the most secure method of protecting information stored on a computer. This blog provides an overview of TPM and how it is used in industrial and medical computers.
Who Created TPM?
Trusted Computing Group (TCG) created TPM in 2003, the first widely used version being TPM 1.1. TPM 1.1 was updated to TPM 1.2, and then to TPM 2.0, the current version and standard. TPM 2.0 is standardized by ISO (International Organization for Standardization) and IEC (International Exchange Commission) under ISO/IEC 11889.
What is TPM?
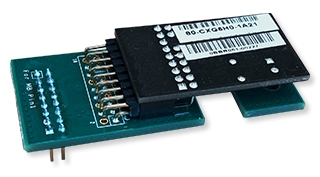
There are five types of TPM: Discrete, Integrated, Firmware, Software, and Virtual. You can read about them in this brief from TCG, but this blog will focus on Discrete TPM, because it is the most common form, it’s the most secure form, and it’s what we use in Teguar computers.
Discrete TPM is in the form of surface mount integrated circuit and is mated to the computer’s motherboard. Other types of TPM are favorable for smaller devices, such as smart phones, as they would not take up valuable real state on smaller computing devices, but they do not have the full tamper proof protection of Discrete TPMs. Many computers, including several product lines from Teguar, come with a TPM chip by default, but the TPM is inactive until it is enabled in the BIOS. It will not affect the computer in anyway, the chip will lay dormant, until activated. However, when activated, a user may notice a slower boot up process with the OS.
What does TPM do?
 TPM is a hardware based security feature and it safeguards the data on your computer. It ensures that no unintended users gain access to your data by either stealing your computer or hard drive or via a software attack or brute force attack. A brute force attack is a “trial and error method,” as explained by SearchSecurity.com, and the attacks “commonly use automated tools to guess various combinations of usernames and passwords until they find the correct input.”
TPM is a hardware based security feature and it safeguards the data on your computer. It ensures that no unintended users gain access to your data by either stealing your computer or hard drive or via a software attack or brute force attack. A brute force attack is a “trial and error method,” as explained by SearchSecurity.com, and the attacks “commonly use automated tools to guess various combinations of usernames and passwords until they find the correct input.”
TCG explains that Discrete TPM protects your device from being hacked, “via even sophisticated methods. To accomplish this, a discrete chip is designed, built and evaluated for the highest level of security that can resist tampering with the chip, including probing it and freezing it with all sorts of sophisticated attacks.”
How does TPM Work?
When you boot a computer, TPM checks the state of the computer and the state of the computer’s environment. If the computer is in a trustworthy state (i.e. it has not been tampered with), it will operate normally. If the computer is not in a trustworthy state, it will not boot, meaning there is no way to access or extract any data from the computer. Things that would trigger an untrustworthy state include:
- the computer hard drive has been placed into another computer (Someone may do this to bypass or deactivate a password protected log-in),
- the computer is being booted and accessed remotely from an unauthorized source,
- the computer has been attacked by a software virus, or
- someone is using a brute-force attack to access the computer.
TPM works by creating encryption codes. Half of the encryption key is stored on the TPM chip and the other half is stored on the computer hard drive. Unless programmed to do so, the TPM chip will never release its half of the encryption key, meaning without that TPM chip, the computer will not boot.
Firmware such as Microsoft’s BitLocker requires TPM. Microsoft explains, “BitLocker uses the enhanced security capabilities of the TPM to make data accessible only if the computer’s BIOS firmware code and configuration, original boot sequence, boot components, and BCD configuration all appear unaltered and the encrypted disk is located in the original computer.” If any of these things are changed, the computer will not boot.
What else can TPM do?
 Besides monitoring the health and security of the computer’s boot environment, other functions of TPM include:
Besides monitoring the health and security of the computer’s boot environment, other functions of TPM include:
- monitoring specific applications on your computer, like email and file systems,
- denying a user access when suspicious changes are detected,
- granting remote access to a trusted third party, and
- verifying system updates for an entire fleet of computers.
These functions are particularly important for industrial and medical computers, as there may be hundreds or even of thousands of computers to update and secure. Without TPM, updates can still be rolled out to a fleet of computers by providing access to the computer network, but this leaves the system vulnerable to hackers. Or, each computer can be updated at the hardware level, manually and individually, which may be very time consuming. TPM ensures the computer fleet is only updated by a verified source.
Where is TPM used?
In a recent blog from TCG, the company says “all Windows laptops, desktops, and servers include a TPM.” TPM has become standard in many consumer grade computers over the last few years, but the blog goes on to explain new frontiers of TPM stating that “in February [2019], the TPM was recommended for use in securing high-risk industrial devices in the newly released international standard IEC 62443-4-2.” TPM prevents hackers from getting sensitive data about your business, and it also prevents them from manipulating or freezing your machines.
In the automotive industry, TPM is used to guard a vehicle’s software. If someone can hack the software of your vehicle, they can control the vehicle’s break system, GPS and more. Likewise, if a hacker gains access to your machinery, they can freeze or alter the machine’s behavior.
In healthcare, TPM is important for protecting patient data. It provides an extra level of security if your computer or tablet is stolen or lost and it protects your IT infrastructure from unauthorized users. While TPM is the hardware focused part of the security measure, Intel VPro is the software that gives a user control and adds more features to TPM. VPro can do a secured remote diagnostic through TPM. For example, say an onboard computer in an ambulance has a problem, as long as there is internet, the hospital IT can run a check and reboot remotely without the ambulance ever returning to the hospital.
To learn more or discuss your project contact us.
Teguar Computers with TPM
| Series | Availability | Version | Note |
| Industrial Computers | Industrial | Industrial | Industrial |
| TP-2920 | Standard | TPM 1.2 | |
| TP-4040 | Standard | TPM 2.0 | (Exception of TP-4040-10) |
| TP-5040 | Standard | TPM 2.0 | (Exception of TP-5040-10) |
| TP-4010 | Option | TPM 2.0 | |
| TP-5010 | Option | TPM 2.0 | |
| TP-5045 | Standard | TPM 2.0 | |
| TSX-5010 | Option | TPM 2.0 | |
| TR-5520 | Standard | TPM 2.0 | |
| TR-0810 | Option | TPM 2.0 | |
| TRT-4380 | Standard | TPM 2.0 | |
| TRT-5180 | Standard | TPM 2.0 | |
| Waterproof Computers | Waterproof | Waterproof | Waterproof |
| TS-4010 | Option | TPM 2.0 | |
| TS-4510 | Option | TPM 2.0 | |
| TS-5010 | Option | TPM 2.0 | |
| TS-5045 | Standard | TPM 2.0 | |
| TS-5610 | Option | TPM 2.0 | |
| TSP-5045 | Standard | TPM 2.0 | |
| TWR-2920 | Standard | TPM 1.2 | |
| TWB-5520 | Standard | TPM 2.0 | |
| Medical Computers | Medical | Medical | Medical |
| TM-5040 | Standard | TPM 2.0 | |
| TM-5557 | Standard | TPM 2.0 | |
| TM-5510 | Option | TPM 2.0 | |
| TM-5010 | Option | TPM 2.0 | |
| TMT-3495 | Standard | TPM 2.0 | |
| TMB-5010 | Option | TPM 2.0 | |
| TMB-5710 | Option | TPM 2.0 |
Sources:
- Arthur W., Challener D., Goldman K. (2015) History of the TPM. In: A Practical Guide to TPM 2.0. Apress, Berkeley, CA doi.org/10.1007/978-1-4302-6584-9_1
- “BitLocker Countermeasures (Windows 10).” (Windows 10) | Microsoft Docs, 27 Feb. 2019, docs.microsoft.com/en-us/windows/security/information-protection/bitlocker/bitlocker-countermeasures.
- Bond, Mike, and Peter Landrock. “The Trusted Platform Module Explained.” Cryptomathic, 12 Sept. 2011, cryptomathic.com/news-events/blog/the-trusted-platform-module-explained.
- Hoffman, Chris. “What Is a TPM, and Why Does Windows Need One For Disk Encryption?” How-To Geek, 11 July 2017, howtogeek.com/237232/what-is-a-tpm-and-why-does-windows-need-one-for-disk-encryption/.
- Rouse, Margaret. “What Is Brute Force Attack? – Definition from WhatIs.com.” SearchSecurity, Jan. 2019, searchsecurity.techtarget.com/definition/brute-force-cracking.
- “TPM 2.0 A Brief Introduction.” Trusted Computing Group, Jun. 2019, trustedcomputinggroup.org/wp-content/uploads/2019_TCG_TPM2_BriefOverview_DR02web.pdf
- “What Can You Do With the Trusted Platform Module (TPM)?” Trusted Computing Group, 1 Jan. 2015, trustedcomputinggroup.org/what-can-you-do-with-the-trusted-platform-module-tpm/.
- “Trusted Computing Enters New Frontiers” Trusted Computing Group, 5 Apr. 2019, trustedcomputinggroup.org/trusted-computing-enters-new-frontiers/.