Safe Information & Technology Computer Hardware Practices for Patient Care
 Health IT security may seem like an overplayed topic, but it is at the core of an oath so many physicians take.
Health IT security may seem like an overplayed topic, but it is at the core of an oath so many physicians take.
The commitment to do no harm, respect secrets entrusted to the caregiver, and practice in conscience and dignity with good medical practice should be major drivers behind technology choices.
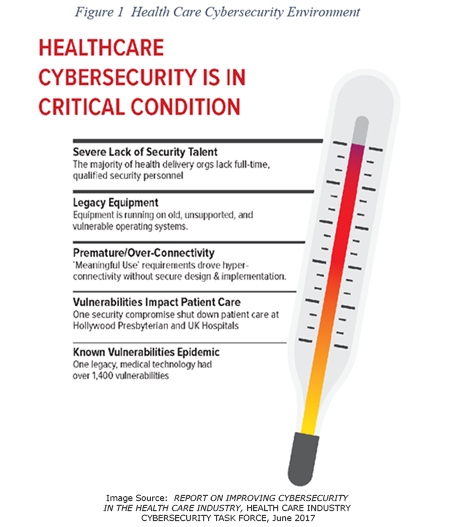
In 2017, the healthcare industry cybersecurity task force created a report on how to accomplish the medical mandate of keeping patients safe in healthcare IT interactions.
In the report, the issue is summarized as follows:
“HHS sees some foundational challenges that need fixing in order to shore up the security of devices, EHRs and legacy operating systems, such as secure development lifecycle, authentication and strategic approaches to product management and maintenance. “
Health Care Industry Cybersecurity Task Force – Report on Improving Cybersecurity in the Health Care Industry, p 28
There are several of these recommendations that can be fulfilled through procuring and maintaining appropriate medical computer hardware. Below are a few examples.
Recommendation 2.1: Secure legacy systems.
Action Item 2.1.1 2 …replace or upgrade systems with supported alternative that have superior security controls where possible.
How Teguar Computers is meeting this challenge:
Every year, Teguar offers you the latest in medical hardware technology which includes the most recent security features on the hardware such as supporting Intel® vPro Hardware and the latest TPM version. There are regular advancements in medical computer security for organizations looking to replace or upgrade systems with superior security controls.
Recommendation 2.3: Increase adoption and rigor of the secure development lifecycle (SDL) in the development of medical devices and EHRs.
How Teguar Computers is meeting this challenge:
Teguar’s industrial and medical computers were designed with long life cycle components and use CPUs on the Intel Embedded Roadmap. When a CPU is designated as embedded, it is guaranteed to be available from Intel for at least seven years from the release date. This gives a long enough life cycle for medical OEMs and healthcare organizations to be able to easily run software security generated updates as the hardware will remain the same for several years.
Recommendation 2.4: Require strong authentication to improve identity and access management for health care workers, patients, and medical devices/EHRs.
How Teguar Computers is meeting this challenge:
Alternative means of authentication, other than traditional passwords, are integrated into Teguar Medical computer products. Single Quick Sign on authentication utilizes various forms of secure technology to login such as a fingerprint reader, barcode scanner, or Smart Card & RFID readers to protect against hacked remote authentication. This way, on-premise security is maintained as the patient is accurately identified as well as the authorized caregiver.
The Cybersecurity Task Force has more than 6 imperatives with dozens of sub-task recommendations and action items along with future considerations. The task may seem daunting, but there are clear objectives that are easily implemented with the right computer hardware.
Secure computer hardware is the foundation on which to lay all other Health IT security concerns.
Previous Article
Teguar Rugged Waterproof Panel PCs are Built for Tough Environments