What are the Benefits of Edge Computing?
This is the second article in Teguar’s Edge Computing Series, defining and discussing Edge Computing and its implementation in industrial applications. The collection was published in 2020 and updated in February 2026. To catch up on the series, start here to read What is Edge Computing.
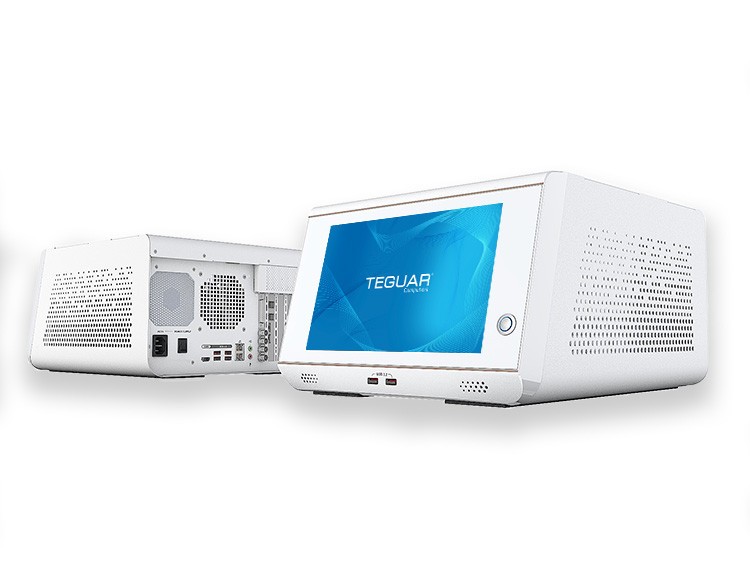
Edge computing moves data processing close to where the data is actually being collected. This means less data is processed in the cloud, and more on the edge device. Today, however, edge computing is no longer just about moving the data processing. It’s important, but it is also increasingly about enabling Edge AI. In healthcare and industry, modern edge systems process sensor, imaging, and operational data locally so organizations can act in real time, reduce bandwidth demands, protect sensitive information, and continue operating even when cloud or network access is limited. Teguar’s current portfolio reflects this shift, with medical-certified all-in-one PCs, medical box PCs, and Edge AI systems designed for demanding environments and AI-enabled workflows.
In this article we’ll dive deep into three main benefits of edge computing, including:
- Faster Decisions
- AI inferencing
- Image/video processing
- Reduced backhaul costs
- Reliability
- Operating through network interruption
- Local failover
- Clinical/industrial continuity
- Security
- Zero Trust
- TPM/root of trust
- Workload identity
- Limited data exposure
There are other benefits not addressed here, such as potential cost savings by reducing your amount of cloud storage and bandwidth, and better scalability, as adding another facility won’t overload your network. To learn more, check out Teguar’s edge computing resources.

Edge Computing Makes Data Processing Faster
Localizing the data processing and storage allows your device to make decisions in milliseconds, rather than several seconds required to transfer between a cloud center. This is most important for applications where a millisecond can make a big difference, such as autonomous cars or precise medical care.
Let’s consider a production line, for example; an industrial edge AI PC (like Teguar’s Regis TB-7393) can use machine vision to detect defects. With a non-edge device, images would need to be sent to the cloud for verification, and the production line would need to move slower accordingly. The on-prem processing, aided by a strong GPU, allows lightning-fast detection for faster production.
Another example where speed is critical is at the point of care. Teguar’s Clarion TM-7200-24 can mount to a medical cart or nurse’s station and supports real-time processing of patient vitals and monitoring other conditions. By eliminating delay in response time, medical staff can act fast and improve patients’ comfort, safety, and outcomes.
For more examples of edge computing applications, check out our article on Edge AI Use Cases.

Edge Computing Increases Reliability
For autonomous systems such as drones, mobile robots, and self-driving vehicles, local compute is not just beneficial—it is essential. Safety-critical decisions cannot depend on network availability, bandwidth, or latency, because any delay in transmitting data to a remote system while waiting for a response can create unacceptable risk. If connectivity is interrupted, degraded, or congested, the machine must still be able to perceive its environment, make immediate decisions, and execute a safe response in real time. In many cases, that means detecting hazards, avoiding obstacles, or safely stopping without relying on offloaded compute. Edge AI ensures these decisions happen at the point of action, where milliseconds matter, making local processing a fundamental requirement for reliable and safe autonomous operation.
Another example where the reliability of edge computing is very important is in food manufacturing. Sensors and measuring devices are placed along the manufacturing line to detect defects. In poultry processing, for example, a laser thermometer might be used to ensure the meat has reached the proper temperature. Within milliseconds, the decision can be made to remove the product from the production line, if it does not meet proper standards. This happens extremely quickly because the computing is being done in the plant, typically in the same room on a computer, or in the same building on a server. If, instead, this data was sent to the cloud and computed elsewhere, the decision might take 2 seconds, rather than 200 milliseconds. This could result in contamination of other products, or at the very least a small delay which adds up over time.
It is beneficial to keep some computing tasks close to the manufacturing plant or vehicle. If the network connection is lost, or slow, your machine can still perform essential tasks. Later, less time sensitive data can be sent to the cloud, such as average temperature of the batch or number of rejects.
Another benefit of distributing some of your data processing and storage is that it can make your business more secure.

Edge Computing Increases Information Security
When he said, “don’t put all your eggs in one basket,” Aesop probably wasn’t thinking about centralized networks and data centers, but his lesson applies here. Relying on one data center to process and store all your business data is risky. If that data center falls victim to a cyberattack, your entire operation could be shut down.
On the other hand, if you decentralize your network, it’s very unlikely that a cybercriminal could steal or manipulate all your data. If you are unfortunate enough to be the victim of a malware attack or data breach, at least only part of your operation will have been compromised. Having the ability to store and process data in multiple locations can give you redundancy that may save your operation when the unexpected occurs.
Edge computing can only make you more secure if you use the right devices. Using a hardware-based security measure, like TPM, is a key requirement for computer hardware used for edge computing.
Edge Computers from Teguar
Check out Teguar’s other edge computing resources to learn about other computer hardware requirements for edge computing. Contact us to discuss your edge project, or request a demo of one of our edge computers.